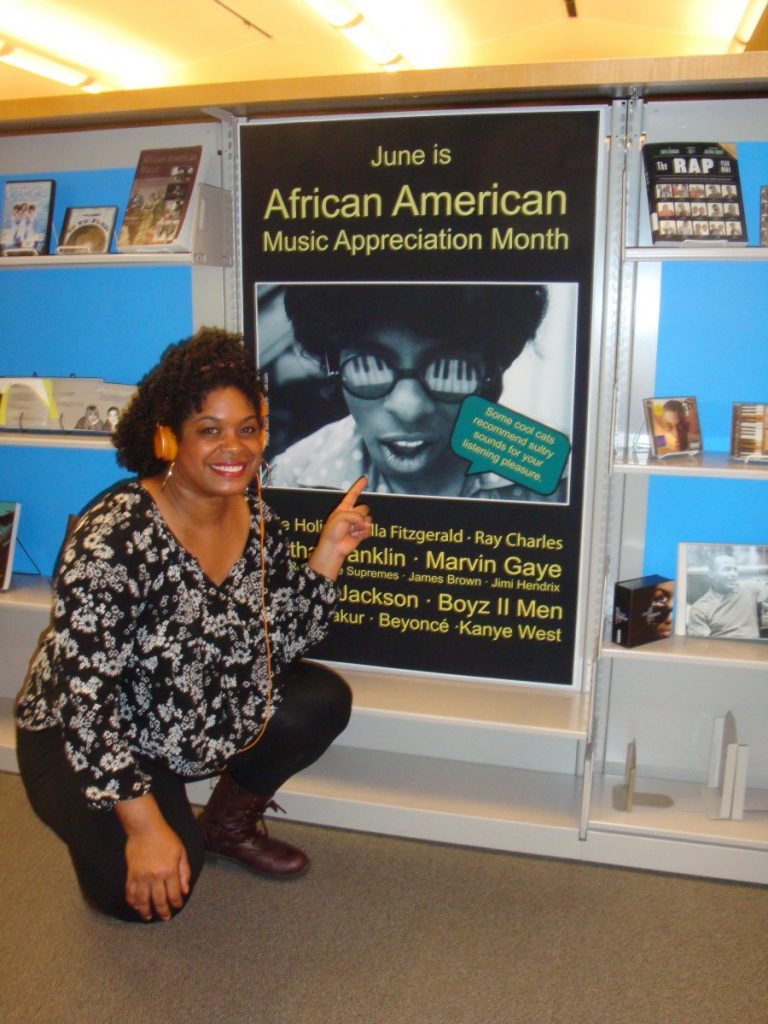
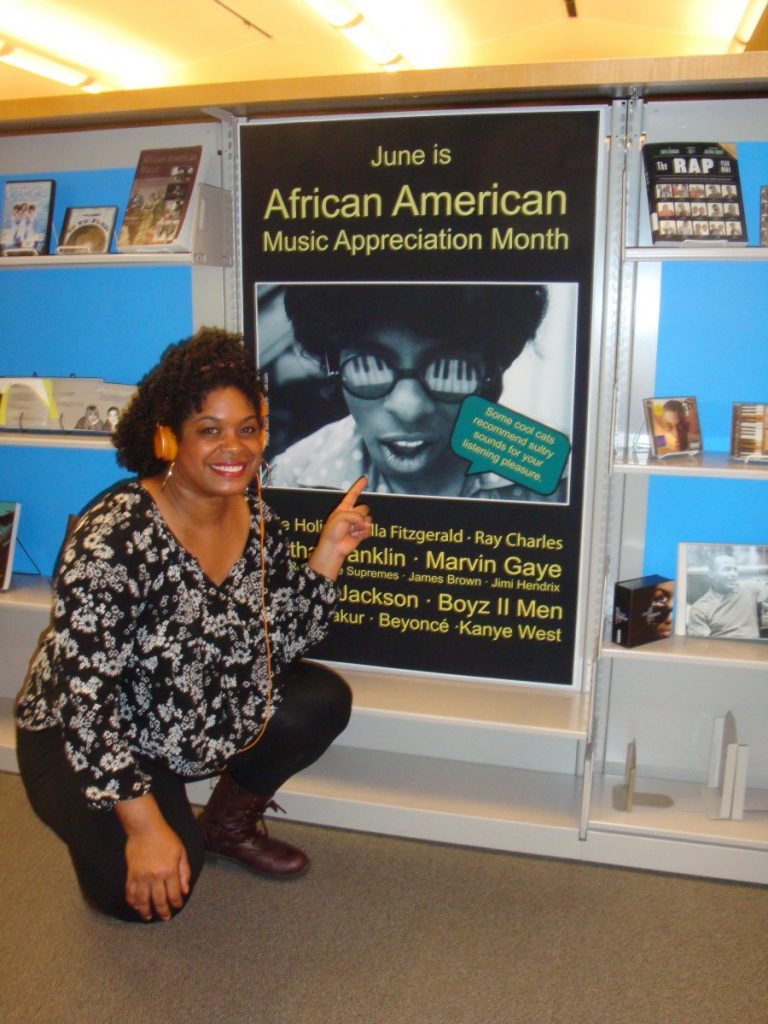
Literatures & Cultures Librarian Katrina Spencer kneels next to a newly installed display featuring African American musics..
I grew up in a very musical household and that identity follows me wherever I go.
Name: Katrina Spencer
Title: Literatures & Cultures Librarian
Hometown: Los Angeles, California
Collaborators: Kat Cyr, Arabella Holzapfel, Amy Frazier, Terry Simpkins, Marlena Evans, Heather Stafford, Innocent Mpoki, Joe Antonioli, Sue Driscoll, Dan Frostman, Kim Gurney, Janine McDonald, Todd Sturtevant, Bryan Carson, Joy Pile, Ryan Clement, multiple student workers, Barack Obama, Jimmy Carter, and others. Many sincere thanks to all of the energy you all have put into this.
Whatcha got goin’ here in the atrium and on the main level of the Davis Family Library?
Of the 23,000+ CDs we have in our collection, we are highlighting over 300 works by and about African American musical artists from June 1st- 22nd. Former President Barack Obama declared June as African American Music Appreciation Month, an initiative first shaped in 1979. President Obama was able to draw further attention to the commemorative month with his 2016 proclamation and the many artists his administration invited to perform at the White House.
Generally speaking, the content spans the 1940s to the early 2000s, including artists from every decade in between. African American music started much earlier than this, but when it comes to largely accessible sound recordings, the early 20th century was perhaps a good place to start in terms of our holdings. However, we do plan to include some very early recordings and have a few monographs that address African American music in the late 1800s- early 1900s.
What motivated you to put this together?
There were so many motivations. First, I have lived now in five states– California, Missouri, Illinois, Wisconsin, Vermont– and while the demographics, landscapes, weather, and food fare change, the consumption of African American music as an avid pastime does not. Scratch that: it’s global. People love the soulful sounds born deep in the South of our country, among pain, oppression, and affliction, within the church, in the Great Migrations to urban spaces, on stage at Harelm’s Apollo Theater, within both Motown’s and Los Angeles’ major recording studios, and shown on MTV and BET. When you tell the story of African American music, you tell the story of our nation.
Second, I attended the Posse Plus Retreat back in February when I was hired and some of the facilitators did a great job of playing music during our set-ups for activities. There I told American Studies professor (and musician) Dr. Will Nash, “I’ll give you all the money in my wallet if you can tell me who’s singing this song.” He thought for a minute and replied, “Is it Brandy and Monica’s “The Boy Is Mine?”” I wasn’t expecting a white man, some 20 years my senior, to know an R&B hit from the 1990s– and I was wrong. Thankfully I was only carrying $1.63 in cash! But that conversation made me realize even more profoundly that music transcends race, class, geography, and other markers we tend to think divide us.
Lastly (and transparently), I love to see people of color taking ownership of our library spaces, myself included. Frequently at predominantly white institutions, people of color and oppressed minorities do not see themselves systematically reflected in the curriculum, the history of their colleges, and/or in the body of faculty and staff. My efforts in the library aim to speak to that scarcity of representation. I’m on a mission to reassert esteem, to remind my audiences that we’re in the 21st century, and that “America” is increasingly and beautifully brown.
How’d you decide what to include?
We crowd-sourced. We started up an Excel file and invited various people on the library staff to add to it. The seven of us rather easily came up with hundreds of works that would fit into our theme. Ha! New recommendations were coming in while we were loading the shelves!
Can I just say that I learned so much in the process of preparing this display? I found out about “soundies,” some of the very first “music videos” of the 20th century that preserve early performances by black artists, that the ubiquitous tune,“The Entertainer,” was composed by a black man, Scott Joplin, and, perhaps most importantly for me, if you ask for help on a project, you’ll get it. This display was nothing if not a collaborative effort.
The layout of the display is a bit unconventional. Can you say a few words about that?
Sure! The idea of adorning our tables (and carrels) with display materials had been brewing for awhile, however, the opportunity to test it out only presented itself this month. The whole point of a display is to draw attention to a theme. While it’s easy to walk past shelving containing “themed” items en route to a study space, it’s harder to miss items in a display that occupy one’s study space. I call it a “guerrilla” method. It’s a more aggressive attempt to engage an audience. (And people are noticing.)
What were some of the challenges in shaping this display?
I wish the students who are normally here during the academic year could see and enjoy the display. Many of them who frequent the Anderson Freeman Center <3 would appreciate the work. However, as we prepare for Reunion, many alumni will likely have an opportunity to encounter it.
We also realize that streaming is perhaps the most popular way for young people to consume music. While we have resources for this (see “Music Online: Listening (North America” within our databases under “M” at go.middlebury.edu/lib), the CD cases and inserts make for great visuals. For those of us wanting to listen to the CDs, know that we have multiple disc drives behind the Circulation Desk to loan out.
This display will last until June 22nd as the whole campus is gearing up for Language Schools and the content includes music in the English language. However, I have made efforts to include artists from the black diaspora like Beny Moré (Cuba) for the Spanish School, Les Nubians (France) for the French School, and Seu Jorge (Brazil) for the Portuguese School.
What do you want people to take away from the display?
I want people taking in the display to think critically about the contributions African Americans have made to this country. Music is merely one of them. Our economic contributions are often hard for people to stomach because they are mired in blood, sweat, and tears. Our scientific contributions experience historical erasures as The Immortal Life of Henrietta Lacks and Hidden Figures suggest. And our political ones are often met with violence, aggression and unpopularity, as the Civil Rights Movements demonstrate, while ultimately forwarding this nation.
How else can we enjoy this effort?
Like our Facebook page. For three weeks we will be sharing videos and trivia that speak to the African American musical experience and history. The content will be loosely chronological and you can follow the evolution of African American music with us.
Last words?
This display is an act of love. We welcome students, faculty, and staff to approach library workers with display development ideas and to continue making the library spaces your own. Also, while the music CDs typically “live” behind the circulation desk, they are still accessible to you. Come check it all out.






 Name
Name Now available for checkout from the Davis Family Library Circulation desk: a family pass (up to 8 people in one vehicle) for free entry into a Vermont Historic Site. This means you can go see and of these historic sites – the Bennington Battle Monument, President Calvin Coolidge, Chimney Point, Hubbardton Battlefield, Senator Justin S. Morrill, Mount Independence, Old Constitution House, President Chester A. Arthur, and Eureka Schoolhouse and Baltimore Covered Bridge – for the bottom line price of zero dollars! At that price, you can’t afford to NOT go learn some history!
Now available for checkout from the Davis Family Library Circulation desk: a family pass (up to 8 people in one vehicle) for free entry into a Vermont Historic Site. This means you can go see and of these historic sites – the Bennington Battle Monument, President Calvin Coolidge, Chimney Point, Hubbardton Battlefield, Senator Justin S. Morrill, Mount Independence, Old Constitution House, President Chester A. Arthur, and Eureka Schoolhouse and Baltimore Covered Bridge – for the bottom line price of zero dollars! At that price, you can’t afford to NOT go learn some history!