According to a security researcher for Linux distributer Red Hat, network hardware sold by several manufacturers failed to properly implement a widely used cryptographic standard, a data-leaking shortcoming that can allow adversaries to impersonate HTTPS-protected websites using the faulty equipment.
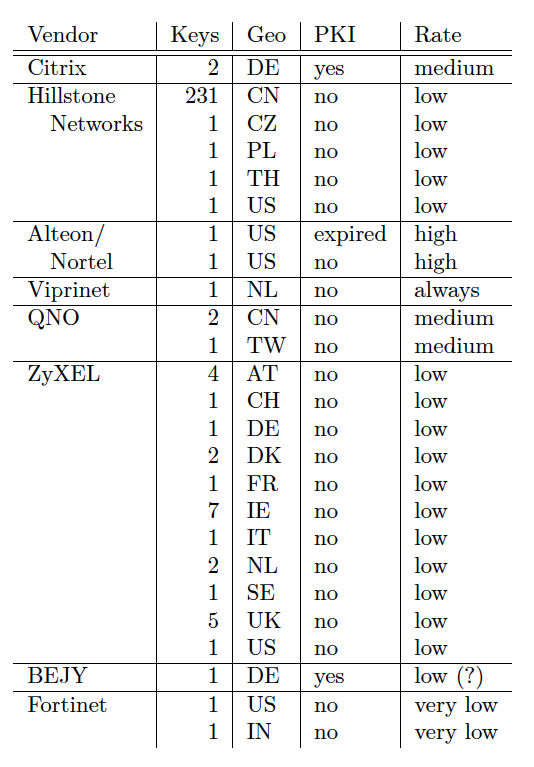
A nine-month scan that queried billions of HTTPS sessions from millions of IP addresses was able to obtain leaked data for 272 keys, reports Red Hat security researcher Florian Weimer in a research paper published this week. Because the scan surveyed only a very small percentage of the overall number of transport layer security protocol handshakes, many more keys and manufacturers are likely to be affected by the leakage. Vulnerable hardware includes load balancers from Citrix as well as devices from Hillstone Networks, Alteon/Nortel, Viprinet, QNO, ZyXEL, BEJY, and Fortinet.
Enter Chinese Remainder Theorem
The leakage is the result of insecure implementations of the RSA public key cryptosystem, which is one of several that HTTPS-protected websites can use to exchange keys with visitors. A 1996 research paper by researcher Arjen Lenstra warned that an optimization based on what’s known as the Chinese Remainder Theorem sometimes causes faults to occur during the computation of an RSA signature. The errors cause HTTPS websites that use the perfect forward secrecy protocol to leak data that can be used to recover the site’s private key using what’s known as a side-channel attack.
